For configuring Certbot with Nginx as quickly and securely as possible.
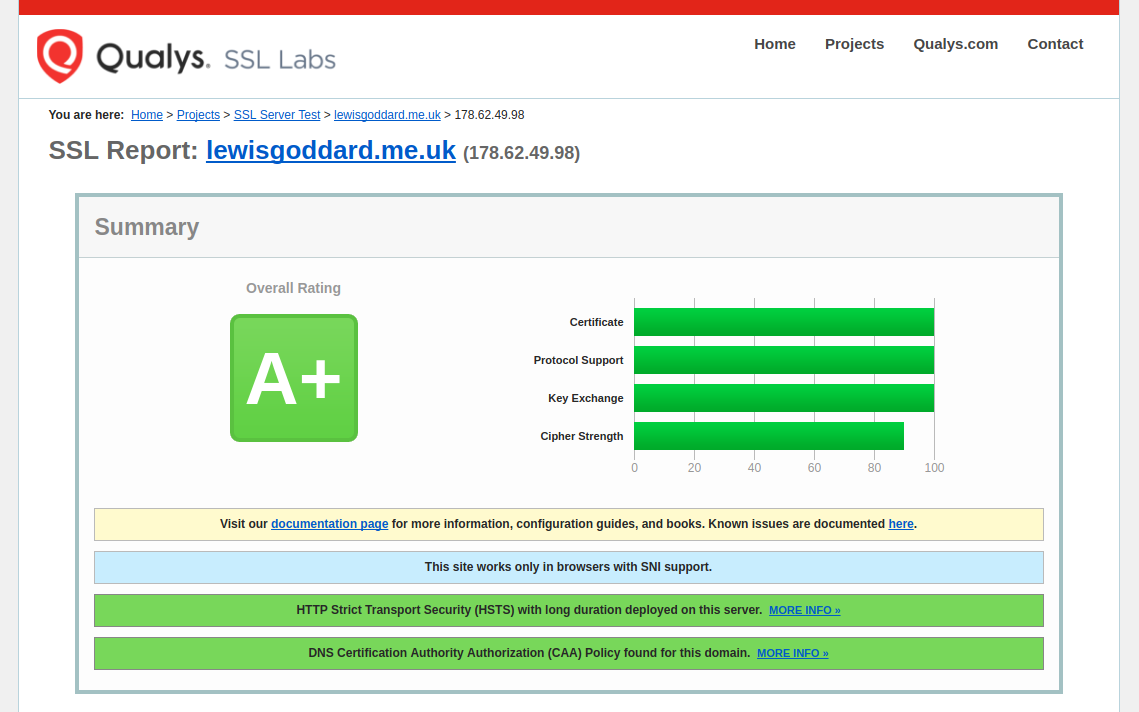
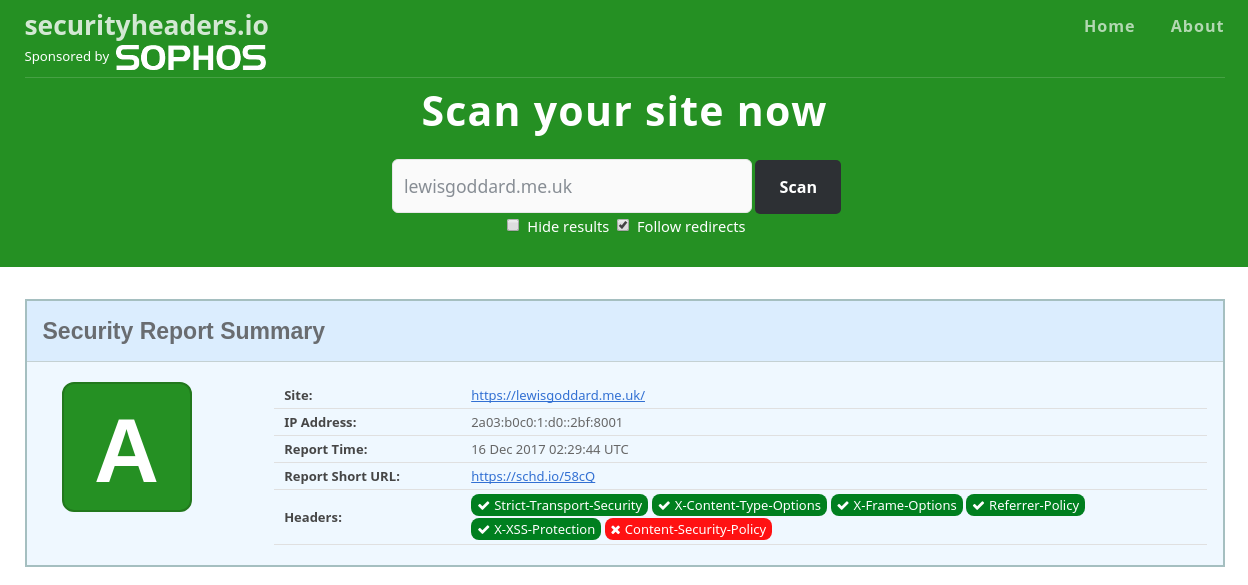
If you want an instant A+ score on Qualys SSL Labs and A score on SecurityHeaders.io, then this is what you'll need to do. You won't need any familiarity with Certbot, Let's Encrypt, the ACME spec, or SSL in general, just basic Nginx configuration.
1. Install Certbot and Clone Bubbly
We'll start off by cloning the project into the home folder with git.
cd &&
sudo apt install git certbot &&
git clone https://github.com/eustasy/Bubbly2. Generate Statics
Generate the static keys once per server.
~/Bubbly/bubbly_generate-tickets.shAs it will warn, this might take a while.
Have a seat.
3. Copy config blocks
When you've gone and made something in the 15 minutes that could well take, or you've just set up a new SSH session, copy the Nginx configuration over to the Nginx area.
~/Bubbly/bubbly_copy-configs.sh4. Configure & Enable Verification
Copy the verification site template and replace the instances of example.com in the file with your actual domain name.
sudo cp /etc/nginx/sites-available/bubbly_http.conf /etc/nginx/sites-available/example.com_http.conf
sudo nano /etc/nginx/sites-available/example.com_http.confUse Ctrl and \ to initiate a search and replace for example.com with your domain.
sudo ln -s /etc/nginx/sites-available/example.com_http.conf /etc/nginx/sites-enabled/example.com_http.conf
sudo nginx -t && sudo service nginx reloadAlternatively, you can simply add include location/bubbly_well-known-passthrough.conf; to an existing site you want to continue working while we upgrade.
5. Fetch Certificates
Fetch your certificates like this:
~/Bubbly/bubbly_renew-ssl.sh -d example.com -d www.example.comIt will ask for the root password, and an email address, so hang around, it shouldn't take more than a few seconds.
Certbot will set up a systemd timer that runs certbot renew automatically twice a day. The --deploy-hook passed by the script is stored in /etc/letsencrypt/renewal/example.com.conf, so Nginx will be reloaded automatically after each successful renewal — no cron job or manual renewal needed.
6. Start using the Certificates
Copy the live site template alongside the verify config you already have. You'll need to more carefully review the [OPTION]s in this file, as you'll also need to change the certificate location to match the domain name you requested. Consider taking a look at the [OPTION]s and [WARNING]s in other linked config files.
sudo cp /etc/nginx/sites-available/bubbly_https.conf /etc/nginx/sites-available/example.com_https.conf
sudo nano /etc/nginx/sites-available/example.com_https.confUse Ctrl and \ to initiate a search and replace for example.com with your domain.
sudo ln -s /etc/nginx/sites-available/example.com_https.conf /etc/nginx/sites-enabled/example.com_https.conf
sudo nginx -t && sudo service nginx reloadKeep example.com_http.conf symlinked in sites-enabled/ permanently. It handles all HTTP traffic (including ACME renewal challenges) so that certificate renewals keep working even if the certificate has already expired.